Hi there
Remember, Your job gives you authority. Your behavior gives you respect!
hostctl - A Cross-platform Hosts Management Tool

While writing internal technical documentation involving domain name consistency issues, I discovered the hostctl tool, which integrates well with the Docker ecosystem…
SSHX - Web-based Secure Collaborative Open Source Command Line Tool
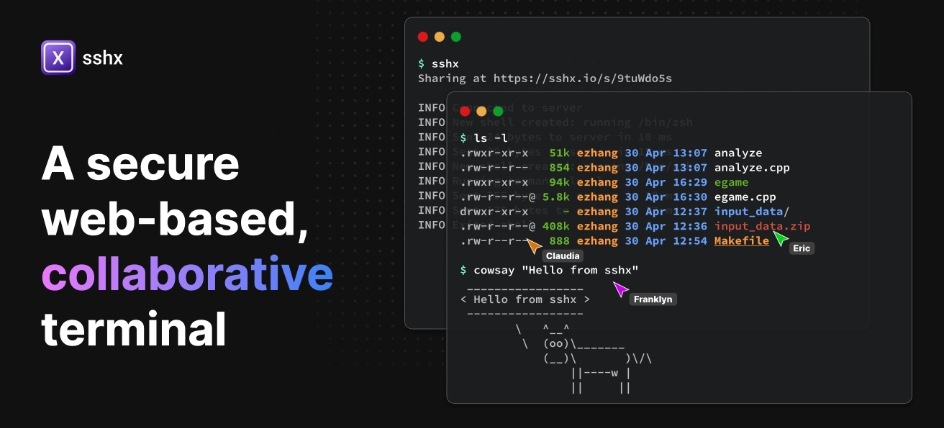
SSHX is a command-line collaboration tool developed in Rust that supports multiple people collaborating online simultaneously and is very simple to use
Quickly Create Go Projects Based on Templates

In the past, to ensure consistency between different projects, we could only manually clone projects and then make incremental modifications according to specific requirements. Now we can achieve this with a single command…
VHS - A Tool for Generating CLI Animations

This is a CLI tool that can generate animations of CLI execution results through configuration files, allowing you to better record your CLI examples
Using Zitadel as an Identity Authentication Center for Go Projects

In a previous article, I mentioned using Zitadel as a unified identity authentication center and integrated it with some projects. Today, I’ll introduce how to integrate Zitadel in Go projects
Extracting WeChat Chat History on macOS

Using technical methods to extract WeChat chat history on macOS, analyze the chat data, and export the required results
OrbStack - The All-in-One Virtual Machine Management Tool for macOS
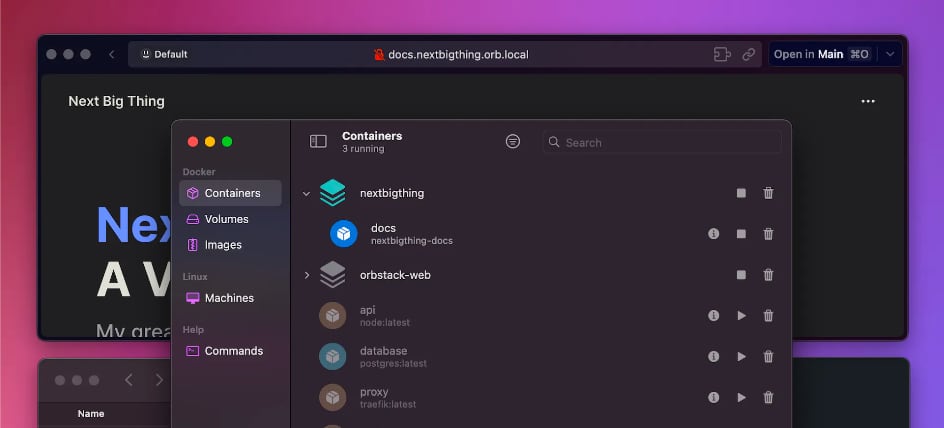
If you’re tired of the slow startup speed of Docker Desktop, the official Docker tool, you might want to try OrbStack
Docker Compose Modularization Feature

After multiple iterations, Docker Compose modularization has finally welcomed this much-needed but previously unimplemented feature.
Default File Opening Methods on macOS

Have you ever experienced double-clicking any type of code file on macOS and it always opens with Xcode? duti is designed to solve this problem.
Cerbos - An Open Source User Authorization Solution
Many enterprise applications require fine-grained permission control, and building a custom authorization system for each application is extremely costly!